The attacker behind the July 30 Curve Finance attack has returned $8.9 million of drained funds, claiming they don’t want to “ruin” the protocols they exploited.
News
The attacker behind the $61 million July 30 Curve Finance attack has returned 4,820.55 Alchemix ETH (alETH), worth approximately $8,889,118, to the Alchemix Finance team and 1 Ether (ETH), approximately $1,844, to the Curve Finance team. The Alchemix Finance protocol alETH-ETH pool on Curve is one of the pools originally exploited.
We have received the test tx funds at 0x9e2b6378ee8ad2A4A95Fe481d63CAba8FB0EBBF9https://t.co/FZraob2wMq
— Alchemix (@AlchemixFi) August 4, 2023
The Curve Finance protocol was attacked through a reentrancy bug on July 30, and over $61 million worth of crypto was lost in the attack. The exploit affected the Alchemix Finance alETH-ETH, JPEG’d pETH-ETH and Metronome sETH-ETH pools. The JPEG’d pool, in particular, was front-run by a miner extractable value (MEV) bot, causing the proceeds from the attack to go to the bot instead of the attacker. The emergency mutisignature wallet suspended all rewards for affected pools on Aug. 2.
Total losses for the exploit were originally estimated at $47 million, but were later updated to $61.7 million.
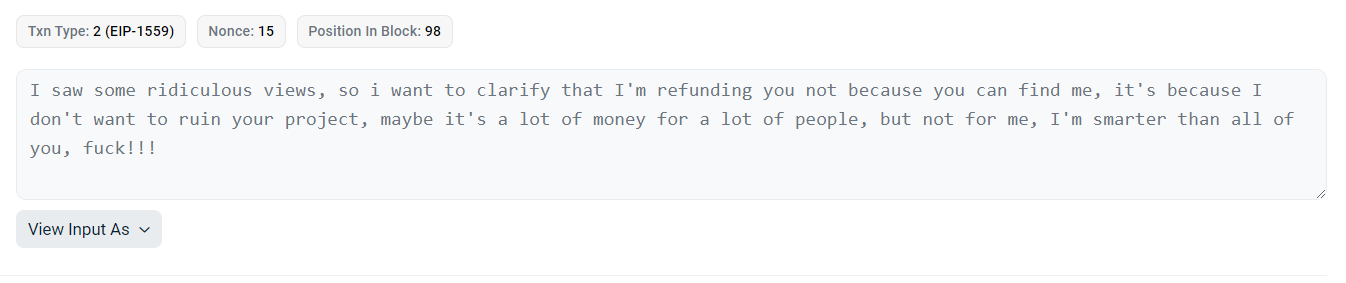
On Aug. 4, at 3:45 pm UTC, the attacker posted a message on the Ethereum network, seemingly directed at the Alchemix and Curve development teams. In it, the attacker claimed they would return the funds, but only because they didn’t want to “ruin” the projects involved, not because the attacker had gotten caught.
At 11:16 am UTC, the attacker returned 1 alETH to the Curve Finance deployer account. Approximately two hours later, they made three separate transfers adding up to 4,820.55 alETH, which were all sent to the Alchemix development team multisig wallet.
Related: Curve, Metronome and Alchemix offering 10% bug bounty on Vyper hack
The total returned funds add up to approximately $8.9 million worth of cryptocurrency. Since the original attack was for over $61 million, these returned funds represent approximately 15% of the total amount drained. However, some funds may have been moved to other addresses and may be returned in separate transactions.
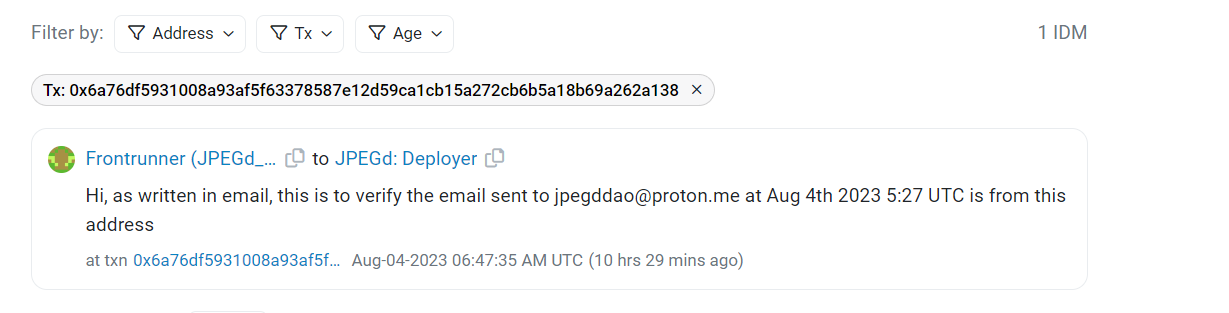
The MEV bot that front-ran the JPEG’d pool attack may also seek to return funds. After transferring the funds to a separate address, it posted a message at 6:47 am UTC that implied its owner was trying to negotiate with the developers through email.
However, the funds from the bot have so far not been returned to any verifiable developer account.




